Solutions For Substations
“The scenario [a physical attack on substations] has an overall major risk profile with a major risk for cross-border impact.”
When we talk about a network solution, we’re describing a system made up of interconnected IP-based components, which can include cameras, speakers, and other devices.
Secure sites
Optimize operations
Protect people
What is a network solution?
Because IP-based devices are connected in a network, they can communicate with each other. That means data can be shared among them, and that rules can be set so that certain events trigger reactions. If we return to the vehicle access example: a camera with analytics to read license plates “recognizes” a vehicle and triggers another device – the access control system – to open the gate.
Offerings
Network Cameras
Other IP devices — wearables, audio, video intercoms, and more
Intelligent analytics
Compatibility with every major VMS
Option of end-to-end management software
Advantages
Quality and reliability
Future-proof innovative technologies
Open systems and easy integration
The highest levels of cybersecurity
Sustainable approach along the entire value chain
Extensive knowledge sharing
The components in a network
Visual Cameras

Audio Equipment

Explosion-protected devices

Intelligent Analytics

Thermal cameras and Radar
Access Control

What is a network solution?
Because IP-based devices are connected in a network, they can communicate with each other. That means data can be shared among them, and that rules can be set so that certain events trigger reactions. If we return to the vehicle access example: a camera with analytics to read license plates “recognizes” a vehicle and triggers another device – the access control system – to open the gate.
Offerings
Network Cameras
Other IP devices — wearables, audio, video intercoms, and more
Intelligent analytics
Compatibility with every major VMS
Option of end-to-end management software
Advantages
Quality and reliability
Future-proof innovative technologies
Open systems and easy integration
The highest levels of cybersecurity
Sustainable approach along the entire value chain
Extensive knowledge sharing
The components in a network
Visual Cameras

Audio Equipment

Explosion-protected devices

Intelligent Analytics

Thermal cameras and Radar
Access Control

"Rather than replacing humans altogether, computer vision empowers operators to identify trends, abnormalities and anomalies, allowing then to take appropriate action in preventing injury and death"
"Rather than replacing humans altogether, computer vision empowers operators to identify trends, abnormalities and anomalies, allowing then to take appropriate action in preventing injury and death"
Solutions for intrusion protection
If a threat actor can physically access a substation, there is virtually no limit to potential damage: malware can be directly introduced to computers and devices, protective relays manipulated, and equipment physically destroyed.”
Improve situation awareness
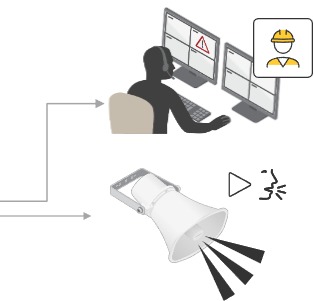
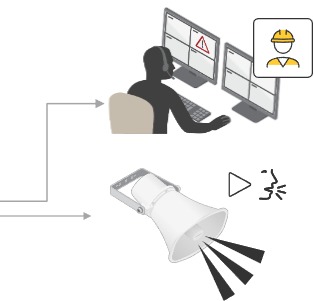
Verify and access threats - and act
Reduce false alarms and physical patrols
Control access to a site or multiple sites
Support training and forensic processes

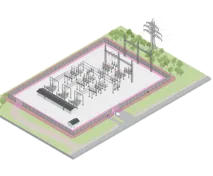
Perimeter protection
Area protection
Access control
Solutions for intrusion protection
If a threat actor can physically access a substation, there is virtually no limit to potential damage: malware can be directly introduced to computers and devices, protective relays manipulated, and equipment physically destroyed.”
Improve situation awareness
Verify and access threats - and act
Reduce false alarms and physical patrols
Control access to a site or multiple sites
Support training and forensic processes

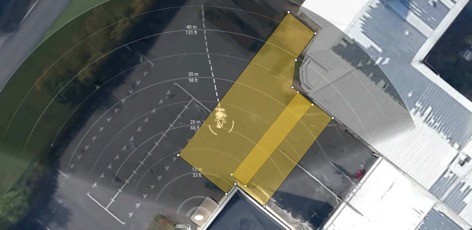
Perimeter protection – buffer zone
Detect and deter before potential intruder gets too close
Detection of presence
A radar pointing outwards detects people and vehicles outside the perimeter.
Alarm is triggered
An alarm event is triggered and sent to an operator, while other devices such as a PTZ camera tracks the object.
Deter unwanted activity
Manually or automatically trigger pre-recorded or live audio messages or siren, with or without light signals.
Physical intervention
Operator initiates physical intervention.

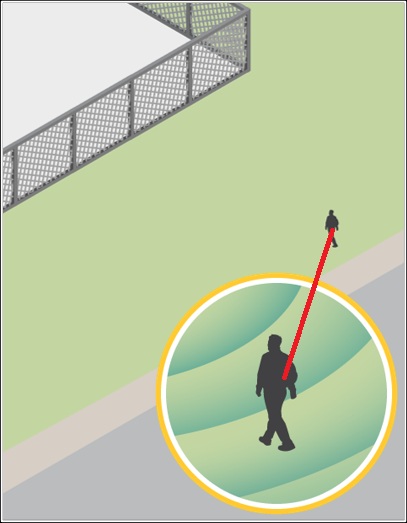
Perimeter protection – buffer zone
Detect and deter before potential intruder gets too close
Detection of presence
A radar pointing outwards detects people and vehicles outside the perimeter.
Alarm is triggered
An alarm event is triggered and sent to an operator, while other devices such as a PTZ camera tracks the object.
Deter unwanted activity
Manually or automatically trigger pre-recorded or live audio messages or siren, with or without light signals.
Physical intervention
Operator initiates physical intervention.

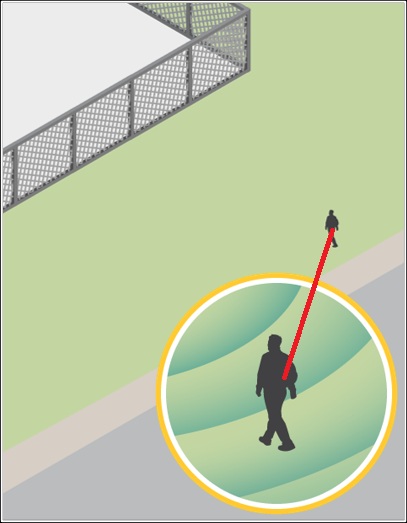
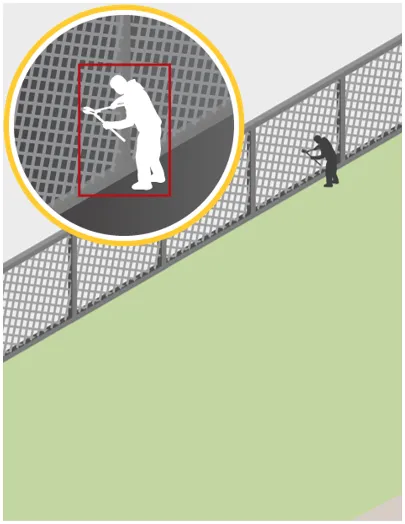
Perimeter protection – fence line
Detect and deter activity on perimeter

Detection of presence
A thermal camera detects people and vehicles close to the perimeter using an application such as Axis Perimeter Defender.
Alarm is triggered
An alarm event is triggered and sent to an operator, while other devices such as a PTZ camera tracks the object.
Deter unwanted activity
Manually or automatically trigger pre-recorded or live audio messages or siren, with or without light signals.
Physical intervention
Operator initiates physical intervention.
Perimeter protection – fence line
Detect and deter activity on perimeter
Detection of presence
A thermal camera detects people and vehicles close to the perimeter using an application such as Axis Perimeter Defender.
Alarm is triggered
An alarm event is triggered and sent to an operator, while other devices such as a PTZ camera tracks the object.
Deter unwanted activity
Manually or automatically trigger pre-recorded or live audio messages or siren, with or without light signals.
Physical intervention
Operator initiates physical intervention.

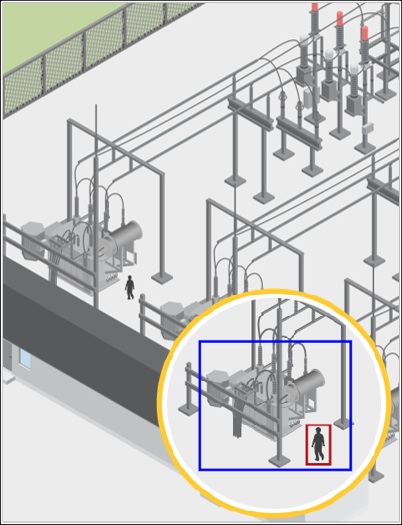
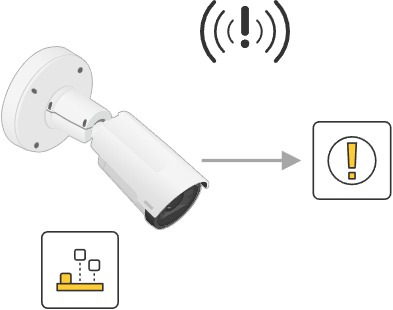
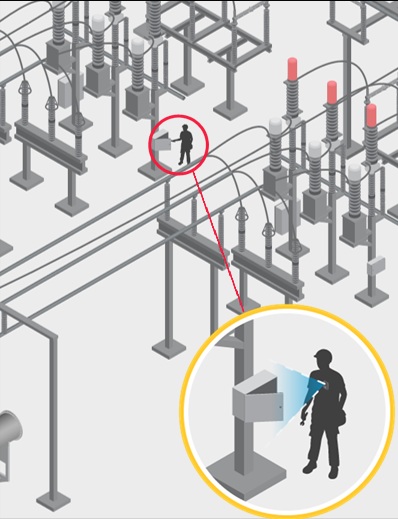
Protecting critical assets
Target surveillance where you need it most
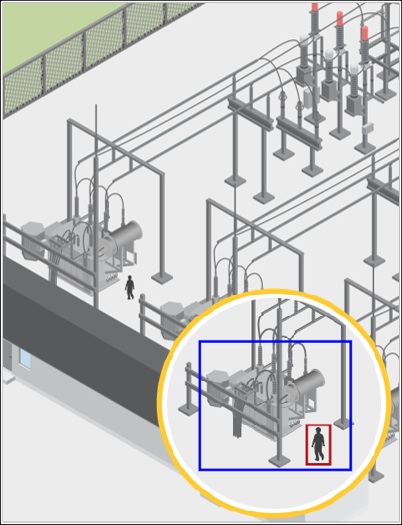
Monitor critical asset
A camera with an analytics application is pointed towards a critical asset with a pre-determined detection zone.
Detect and alert
Someone approaching the critical asset will be detected, and an alert is sent to the operator.
Deter unwanted activity
A prerecorded audio message or siren is automatically triggered (with or without light signals) and/or the operator sends a live audio messages.
Physical intervention
Operator initiates physical intervention.

Protecting critical assets
Target surveillance where you need it most
Monitor critical asset
A camera with an analytics application is pointed towards a critical asset with a pre-determined detection zone.
Detect and alert
Someone approaching the critical asset will be detected, and an alert is sent to the operator.
Deter unwanted activity
A prerecorded audio message or siren is automatically triggered (with or without light signals) and/or the operator sends a live audio messages.
Physical intervention
Operator initiates physical intervention.

Access control – people
Secure sites, buildings and offices from unwanted visitors
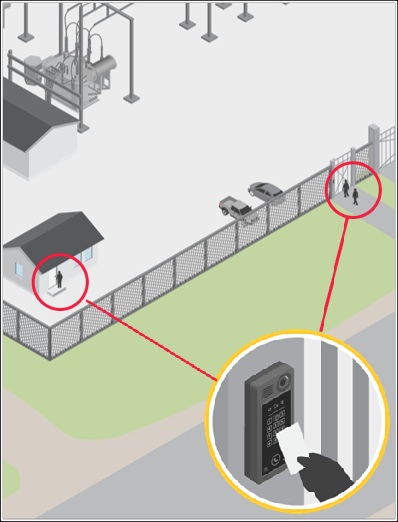
Card or code for entry
Staff or visitors use cards, keycodes or QR codes to enter site or buildings.
Check if user is registered
System checks the database to see if the user is registered and permitted in the specific location.
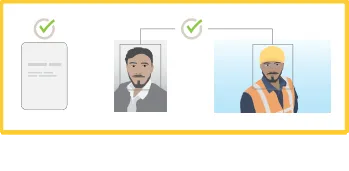
Access is granted or denied
Depending on privileges access is either permitted or denied.
Access control – people
Secure sites, buildings and offices from unwanted visitors
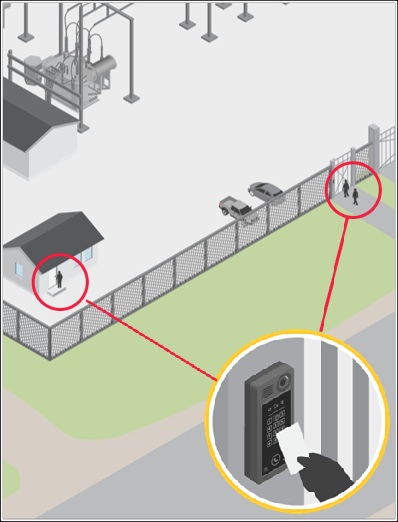
Card or code for entry
Staff or visitors use cards, keycodes or QR codes to enter site or buildings.
Check if user is registered
System checks the database to see if the user is registered and permitted in the specific location.
Access is granted or denied
Depending on privileges access is either permitted or denied.
Access control – vehicles
Secure sites, buildings and offices from unwanted visitors

Card or code for entry
Staff or visitors use cards, keycodes or QR codes to enter site or buildings.

Check if user is registered
System checks the database to see if the user is registered and permitted in the specific location.

Access is granted or denied
Depending on privileges access is either permitted or denied.
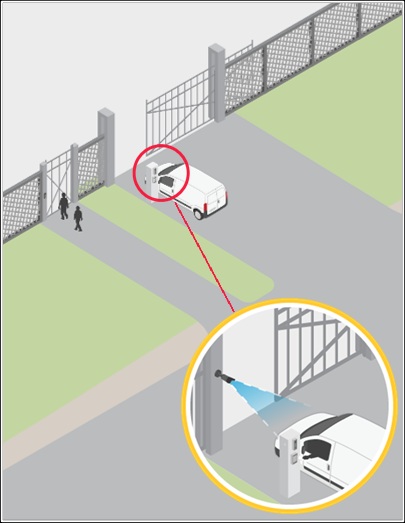
Access control – vehicles
Secure sites, buildings and offices from unwanted visitors
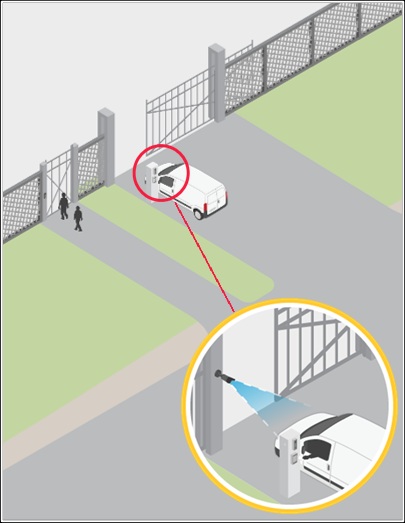
Detect vehicle and read license plate
Car approaches gate and camera with embedded analytics reads license plate.

Analyze license plate data
Plate is analyzed and result is compared to an allow list.

Automatic and manual access
If the visitor is known the gate opens automatically for them.
In the event the visitor is unknown the site administrator is provided the information needed to either deny or allow access.

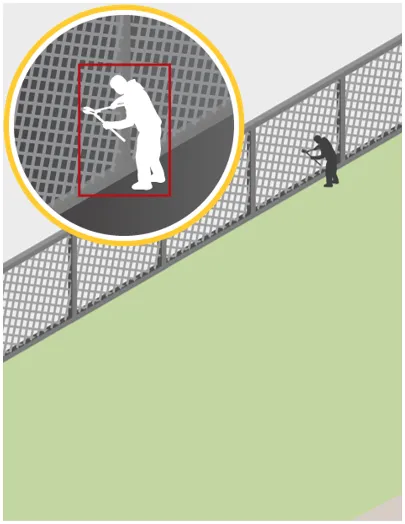
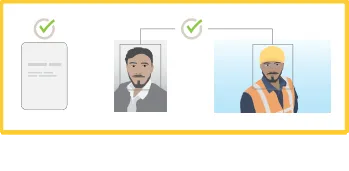
PPE detection
Ensure safety compliance with PPE detection
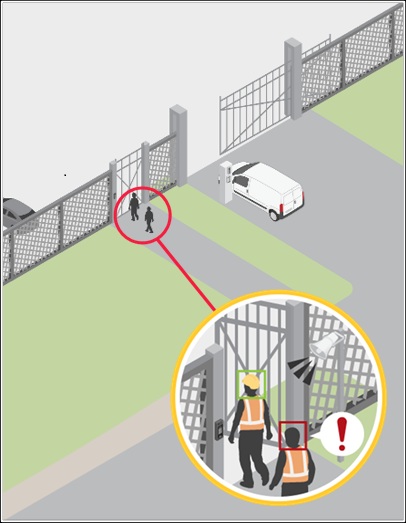
Detect and alert
Camera captures and processes images, using analytics to search for PPE compliance. Non-compliance triggers an alert.
Automated response
Pre-recorded message is triggered.
Physical intervention
Operator initiates physical intervention for adherence.
Manual response
Operator evaluates the information and initiates appropriate response.
Audio alerts
Operator triggers pre-recorded or live audio message.
PPE detection
Ensure safety compliance with PPE detection
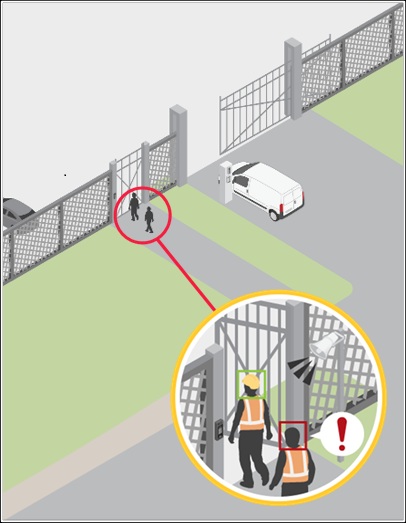
Detect and alert
Camera captures and processes images, using analytics to search for PPE compliance. Non-compliance triggers an alert.
Automated response
Pre-recorded message is triggered.
Physical intervention
Operator initiates physical intervention for adherence.
Manual response
Operator evaluates the information and initiates appropriate response.
Audio alerts
Operator triggers pre-recorded or live audio message.
Maintenance verification
Additional safety and peace of mind
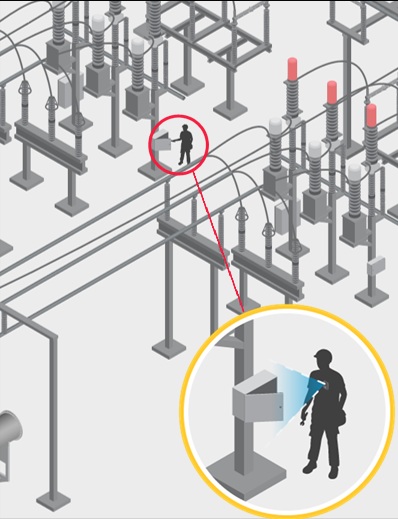



Document and monitor processes
Use body worn camera to monitor maintenance process and provide insights.
Better safety awareness
From a safety perspective, monitoring staff working on site provides a possibility to respond in the event of an emergency.
Manual response
The operator evaluates the information and initiates appropriate response.
Maintenance verification
Additional safety and peace of mind
Document and monitor processes
Use body worn camera to monitor maintenance process and provide insights.
Better safety awareness
The operator evaluates the information and initiates appropriate response.
Manual response
From a safety perspective, monitoring staff working on site provides a possibility to respond in the event of an emergency.
Contact Us for a FREE consultation.
Contact Us to find out more
Reach out now, and we will schedule an introduction call with you. Where we will discuss your system needs and expectation, and share our expert opinion with you.

Visit our Experience Center
The AXIS Communications Experience Center, located in the heart of Fort Lauderdale, offers a personalized, hands-on environment where you can explore the full range of AXIS technologies up close. Their team provides expert guidance, live demonstrations, and answers to all your questions—giving you a clear, confident understanding of the right solutions for your property.
We always look forward to welcoming our customers and making every visit a great experience. Schedule a visit with us at any time—coffee and snacks are on us.
OUR SERVICES
OUR CONTACTS
EXPERIENCE CENTER
EXPERIENCE CENTER
401 E Las Olas Blvd,
Fort Lauderdale,
FL 33301
OUR CONTACTS
© Copyright 2026. Baltic Service LLC. All Rights Reserved.


OUR CONTACTS
© Copyright 2026. Baltic Service LLC. All Rights Reserved.



